What Is Mobile App Security Testing?
Mobile devices accounted for 52.6% (Statista, 2019) of Internet traffic in 2019. With 5G technology emerging, this is predicted to increase fivefold by the end of 2024 (https://www.ericsson.com/en/5g/what-is-5g).
Mobile applications are becoming ever more prevalent in our daily lives, and many services are moving to a mobile-first strategy.
Anytime a (relatively) new technology like mobile computing is introduced, security concerns arise specific to that technology. Mobile applications are arguably more secure than their desktop counterparts due to controls such as sandboxing, user privacy controls, and limited access to the OS’s low-level APIs. However, there is a unique set of security issues that mobile application creators frequently overlook.
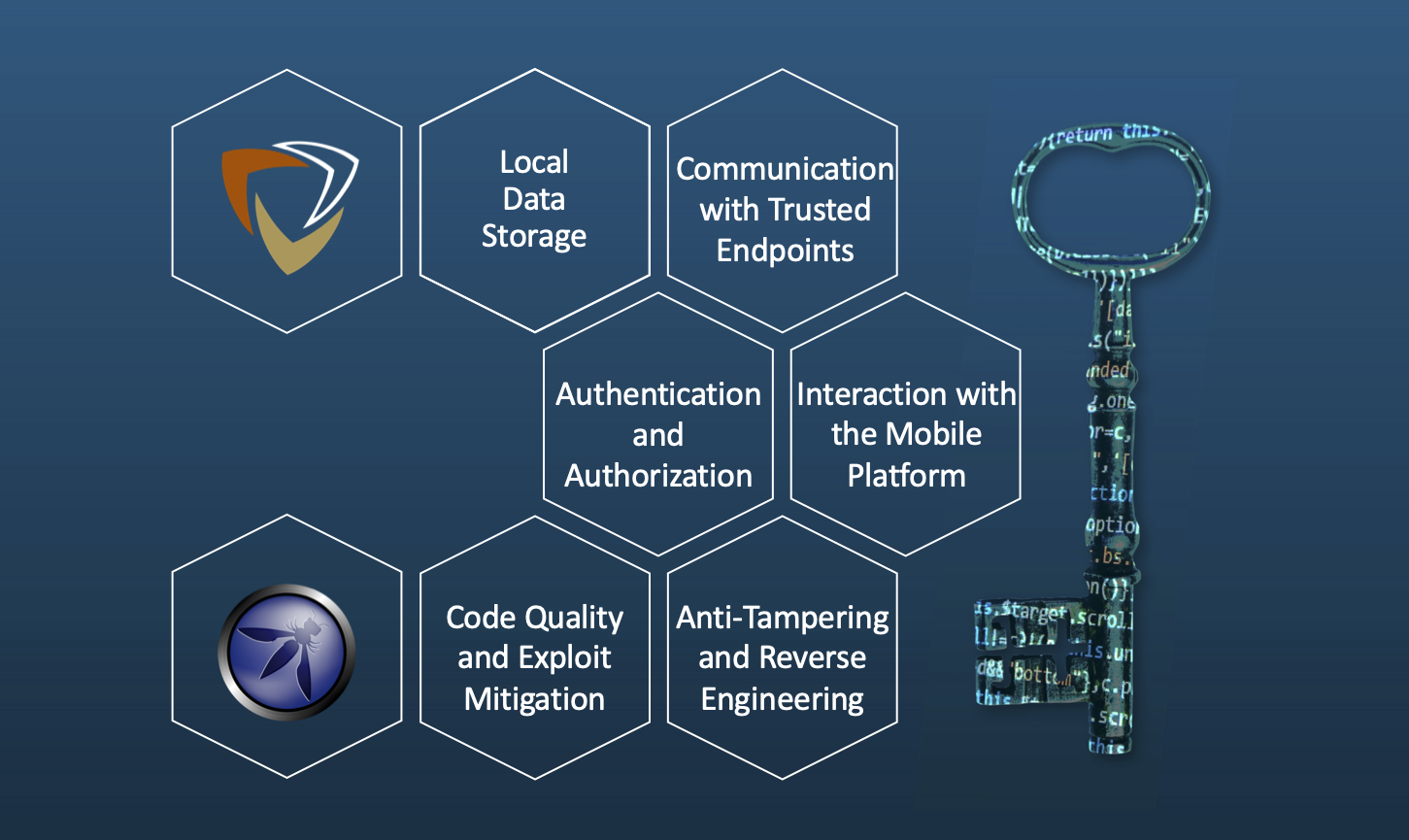
The OWASP MATG (Mobile Application Testing Guide) defines the following key areas in mobile security:
- Local Data Storage - if an app does not properly manage its sensitive data storage, the data can be leaked to other applications, cloud storage, backups, and keyboard cache. Also, a mobile device is easier to physically lose or steal since its small and carried everywhere by the user.
- Communication with Trusted Endpoints - mobile devices constantly connect to various WiFi and cellular networks, which a malicious actor could control. Therefore, mobile applications must properly utilize encryption protocols like TLS for network communications.
- Authentication and Authorization - most mobile applications use a remote service to manage user authentication and authorization. If the remote services do not correctly handle the authentication and authorization, or if essential parts of the authentication flow are performed on the device instead of via the remote service, an attacker may be able to bypass these controls. Also, session tokens granted to mobile devices typically have a much longer expiration than a desktop or web application.
- Interaction with the Mobile Platform - mobile applications are constrained by app permission systems enforced by the operating system. These prevent the applications from accessing data and functions that they are not explicitly granted access to. However, these have their own shortcomings, and if they are not correctly used, could expose sensitive data to other applications.
- Code Quality and Exploit Mitigation - despite many protections in place by mobile OSs to prevent security issues, sloppy code will still result in vulnerabilities. While many problems such as buffer overflows and XSS are limited on mobile devices, there are still cases where attacks like these are possible and can have meaningful impacts.
- Anti-Tampering and Reverse Engineering - many developers assume that the mobile application bundle protects all sensitive data and source code. However, experienced attackers can bypass many of these controls and bypass client-side protections, allowing them to steal sensitive data such as API keys and credentials. If security controls that the developers should implement on a remote backend service are implemented in the mobile application, an attacker can often bypass these protections.
How can these security pitfalls be avoided? Application owners and developers should consider mobile application security during all steps of the design, development, testing, and deployment process. Whether the application is fully deployed or a proof-of-concept MVP, security testing is a great way to determine the application’s current security posture and identify areas that need improvement.
How Are Mobile Applications Tested For Security?
Mobile application security testing is not so different from web, cloud, or network security testing, at least from a high level. While the specifics of the test might be different, the overall methodology remains consistent. For example, here is an outline of Pensive Security’s security testing methodology:
- Pre-engagement - establish rules of engagement, communicate scope, determine the timeline of the test
- Planning - develop a security assessment plan
- Target Reconnaissance and Enumeration - identify key target components, passive and active enumeration of in-scope targets
- Vulnerability Identification - examine services, identify component relationships, understand logic flows, enumerate high-risk components, identify potential vulnerabilities, and vulnerability scan
- Exploitation - use gathered information, tools, and scripting to exploit flaws and circumvent
controls - Reporting - explain current security posture, provide overall risk score, present an attack narrative explaining our entire testing process including successful and failed tests, clearly identify what was tested and what was not tested, detail security issues, create easy to recreate proof of concept exploits, provide remediation suggestions
- Retesting - ensure reported issues are remediated or are accepted as a risk by the customer
As you can see, security testers could apply the same high-level methodology to a web or desktop application security test.
How is Mobile App Testing Different?
With mobile application security testing, the difference is in the details. While web applications typically suffer from vulnerabilities such as XSS and CSRF, these same attacks are usually not possible within a mobile application. Instead, the security test more or less amounts to focusing on the “key areas” outlined above and understanding the differences between mobile applications and other technologies.
For example, a common starting point for many web application security tests is to perform automated and manual analysis of the client-side code to determine if any secrets are stored and how it communicates with the backend server. Similarly, tools exist to perform automated scans of mobile application bundles, extract sensitive data, identify endpoints that the application communicates with, and more.
During a mobile application security test, the testing team will enumerate the application as much as possible to determine how the application works and what functionality the application supports. The team will then assemble a testing plan based on each component’s potential risk, prioritizing the highest risk areas first. Then specific mobile app test cases for each of the “key areas” will be performed to identify vulnerabilities and develop exploits.
Our Mobile App Security Testing Checklist
At Pensive Security, we prefer to use standardized and open-source resources when developing and executing our security tests. Specifically, for mobile application security testing, we base our testing on the OWASP MASVS (Mobile Application Security Verification Standard) and the OWASP MATG (Mobile Application Testing Guide). OWASP has combined the common elements of these two resources into a checklist that we use to ensure standard and consistent coverage during testing.
What is the OWASP Mobile Application Security Verification Standard?
We’ve already discussed the MATG (Mobile Application Testing Guide) from OWASP, but what about the OWASP MASVS (Mobile Application Verification Standard) we mentioned? The goal of the MASVS (from the standard itself) is to:
- Provide an industry-standard mobile app security review
- Clarify the role of mobile security mechanisms and identify ways to test their effectiveness
- Create a set of requirements for architects and developers to develop secure mobile apps
- List recommendations for securing application components in different use cases
In addition to a standard mobile application penetration test, Pensive Security also provides MASVS testing and an attestation that a mobile application adheres to the standard’s requirements.
In Conclusion…
Mobile applications will continue to be a large part of the technology landscape for years to come. Mobile application usage will likely continue to grow and become even more prevalent. With every new technology, new ways of designing, developing, deploying, and testing must be created and performed. While security testing mobile applications is similar to other types of security testing from a high-level, the test’s specific details vary immensely. We use open-source resources like the OWASP MATG and MASVS to ensure that the security tests we perform are high-quality and standardized.
Need Your Mobile Application Tested By Professionals?
If you have an existing mobile application or are in the process of designing and developing a new one, let us know! We have a long history of performing superior security testing across many technologies, and mobile application testing is one of our most popular services. Want to learn more about how you can secure your mobile application with a security test? Contact us today, and we’ll show you.